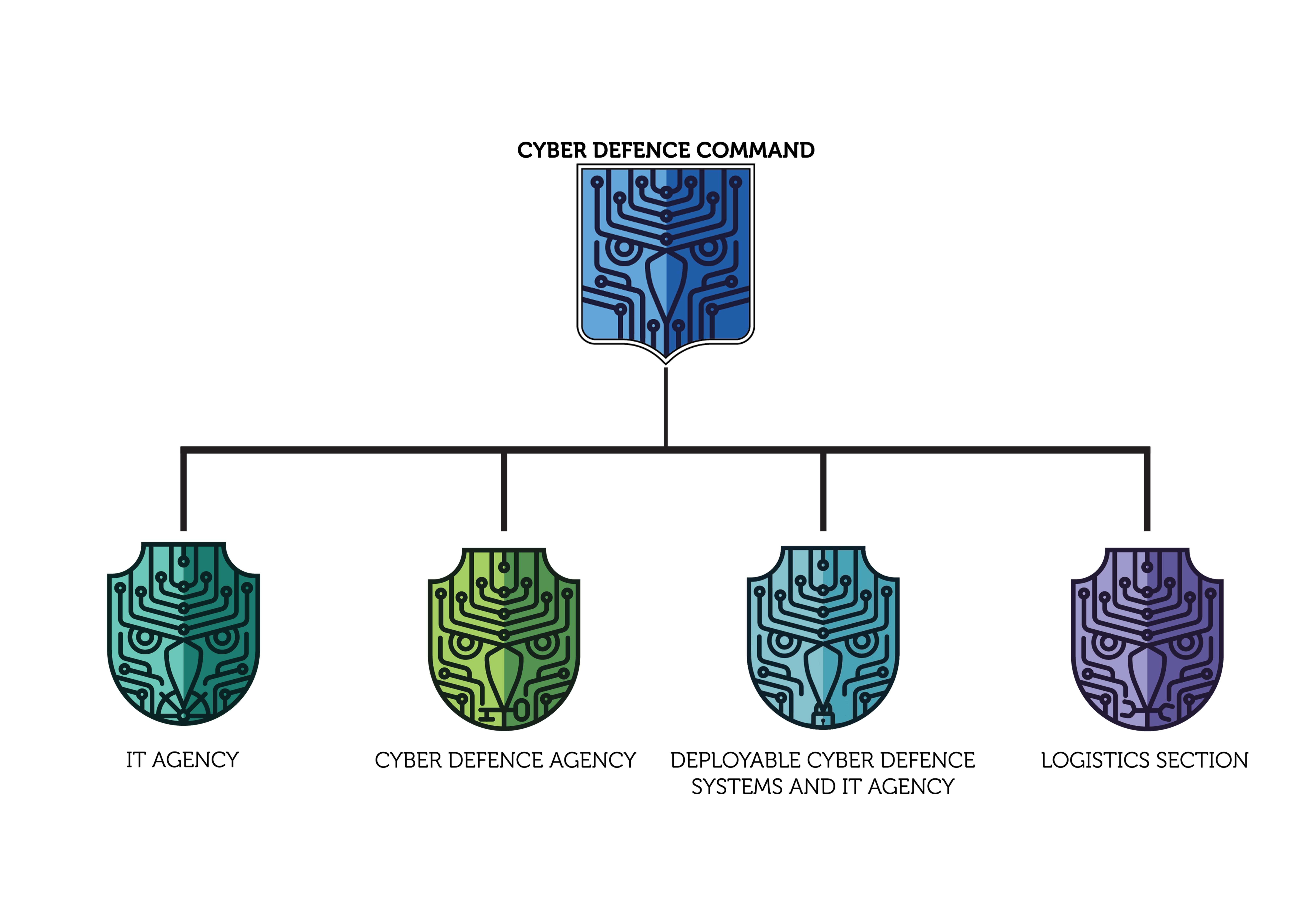
The Cyber Defence Command is part of the forces that actively participate at the Romanian Military missions’ accomplishment. In this context, it has the role to plan, organize, control and conduct cyber space operations, in order to support the networks functional resilience and to generate effects in support of the joint forces, within both the national and allied environment. At the same time, the command provides network management and development and Information Technology services.
In the field of cyber security and defence, the Cyber Defence Command has the following responsibilities:
In the field of cyber security and defence, the Cyber Defence Command has the following responsibilities:
- Cyber incidents management;
- Secure the protection and resilience of military networks against cyber threats;
- Identification and evaluation of cyber threats and risks;
- Plan, organize, control and conduct cyber space operations;
- Integration of the cyber operations in the joint operations of the Romanian Armed Forces;
- Military and interdepartmental cooperation, national and international;
- Contributions to concept and legislation development in the cyber field;
- Contributions to the development and optimization of military and national cyber defence capabilities.
- Secure the functionality and resilience of data within the military cyber networks;
- Development, implementation and management of IT applications for the users within the Ministry of National Defence (MoND);
- Management of software licenses for the MoND;
- Verification and validation of IT applications used within the MoND networks;
- Implementation of IT models and processes that provide the functionality of the military cyber services and networks.

